Risk Management Frameworks | Vibepedia
Risk Management Frameworks (RMFs) are structured methodologies designed to identify, assess, and control threats to an organization's assets, operations, and…
Contents
Overview
The genesis of formal Risk Management Frameworks can be traced back to the stringent security requirements of military and intelligence agencies. Early precursors emerged from the need to protect sensitive information systems, particularly during the Cold War era. The DoD and later the NIST played pivotal roles in codifying these processes. NIST's publication of Special Publication 800-37, 'Risk Management Framework for Information Systems and Organizations,' marked a significant milestone, formalizing a six-step process that integrated security and risk management into the entire system development lifecycle. This framework built upon earlier efforts like the CVE initiative and the foundational principles of information security laid out by pioneers like Dorothy Denning.
⚙️ How It Works
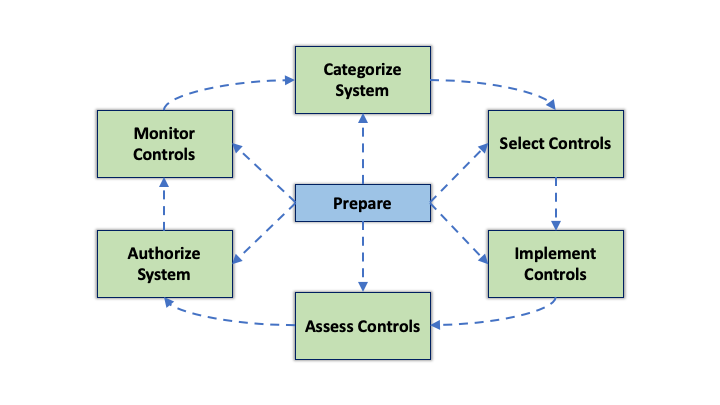
At their core, RMFs operate through a cyclical process, typically involving six key steps: Categorize, Select, Implement, Assess, Authorize, and Monitor. First, an organization must categorize its information systems and assets based on potential impact. Next, it selects appropriate security controls tailored to these categories. These controls are then implemented and integrated into the system. An independent assessment follows to determine the effectiveness of the implemented controls. Based on the assessment results, an Authority to Operate (ATO) is granted, signifying acceptance of the residual risk. Finally, continuous monitoring ensures that controls remain effective and that the system adapts to evolving threats, a process often managed via SIEM tools.
📊 Key Facts & Numbers
Globally, the adoption of RMFs is substantial. The global cybersecurity market, heavily influenced by RMF adoption, was valued at over $200 billion in 2023 and is projected to exceed $300 billion by 2027, underscoring the economic significance of robust risk management. Furthermore, compliance with frameworks like the GDPR often necessitates adherence to RMF principles, affecting over 450 million EU citizens.
👥 Key People & Organizations
Key figures in the development and promotion of RMFs include Kevin St. Arnaud, a significant contributor to NIST's RMF evolution, and Robert J. St. Louis, whose early work on information security risk analysis laid crucial groundwork. Organizations like NIST, the ISO, and the CISA are central to defining and disseminating these frameworks. In the private sector, companies such as IBM and Deloitte offer consulting services and develop tools to help organizations implement RMFs. The Cloud Security Alliance (CSA) also provides guidance on applying RMF principles to cloud environments, demonstrating a broad ecosystem of contributors.
🌍 Cultural Impact & Influence
The influence of RMFs extends far beyond their initial cybersecurity focus. They have become foundational to enterprise risk management (ERM) strategies across industries, shaping how businesses approach financial, operational, and strategic risks. The structured, repeatable nature of RMFs has inspired similar frameworks in fields like project management and business continuity planning. The widespread adoption of RMFs has also fostered a global dialogue on security and resilience, influencing regulatory bodies and international standards. The principles embedded in NIST's RMF can be seen echoed in frameworks adopted by the ENISA and the MAS in Singapore, illustrating a convergence of best practices.
⚡ Current State & Latest Developments
In 2024, the landscape of RMFs is characterized by an increasing emphasis on automation and artificial intelligence. Organizations are leveraging AI-powered tools for continuous monitoring, threat detection, and automated control selection within frameworks like NIST's RMF. The integration of privacy considerations, driven by regulations like CCPA and GDPR, is also becoming more deeply embedded. Furthermore, the rise of supply chain attacks has spurred a greater focus on third-party risk management within RMFs. Emerging standards, such as the ISO 27001 updates, reflect these evolving priorities.
🤔 Controversies & Debates
A significant debate surrounds the rigidity versus flexibility of RMFs. Critics argue that overly prescriptive frameworks like NIST's RMF can be burdensome for smaller organizations or those in rapidly changing sectors, leading to 'check-the-box' compliance rather than genuine risk reduction. Conversely, proponents emphasize that the structured nature is essential for ensuring consistent security posture and meeting regulatory mandates, especially for large enterprises and government bodies. Another point of contention is the effectiveness of continuous monitoring; while theoretically ideal, its practical implementation often faces resource constraints and challenges in accurately interpreting vast amounts of data generated by SIEM systems. The debate over the true ROI of RMF implementation, particularly in terms of quantifiable risk reduction versus compliance costs, remains ongoing.
🔮 Future Outlook & Predictions
The future of RMFs points towards greater integration with emerging technologies and a more proactive, predictive approach to risk. Expect to see deeper incorporation of AI and machine learning for real-time risk assessment and automated response mechanisms, moving beyond the current NIST RMF's six steps. The concept of 'zero trust' architecture is likely to become a core tenet, fundamentally reshaping how controls are selected and implemented. Furthermore, as the global threat landscape evolves, RMFs will need to adapt to address novel risks, including those posed by quantum computing and advanced AI-driven cyberattacks. The trend towards 'security-by-design' and 'privacy-by-design' will also solidify, making RMFs an integral part of the initial conceptualization phase of any new system or product.
💡 Practical Applications
RMFs are not just theoretical constructs; they have tangible applications across virtually every sector. In finance, they are critical for complying with regulations like SOX and protecting sensitive customer data. Healthcare organizations use RMFs to safeguard patient records under HIPAA. Technology companies employ them to secure software development lifecycles, protect intellectual property, and ensure the integrity of cloud services. Government agencies rely heavily on frameworks like NIST's RMF to secure critical infrastructure and national security systems. Even in less obvious fields, like EdTech, RMF principles are applied to protect student data and ensure the reliability of learning platforms.
Key Facts
- Category
- technology
- Type
- topic