Buffer Overflow | Vibepedia
A buffer overflow occurs when a program tries to write more data to a fixed-size buffer than it can hold, overwriting adjacent memory. This vulnerability…
Contents
- 🛡️ What is a Buffer Overflow?
- 📜 Historical Context & Early Exploits
- ⚙️ How Buffer Overflows Actually Work
- 💥 Types of Buffer Overflows
- 🚨 The Impact: What Happens When One Occurs?
- 🛡️ Defenses & Mitigation Strategies
- ⚖️ Legal & Ethical Ramifications
- 📈 The Future of Buffer Overflow Exploitation
- ⭐ Vibepedia Vibe Score & Controversy Spectrum
- 💡 Practical Advice for Developers & Users
- Frequently Asked Questions
- Related Topics
Overview
A buffer overflow occurs when a program tries to write more data to a fixed-size buffer than it can hold, overwriting adjacent memory. This vulnerability, first documented in the early 1970s, allows attackers to inject malicious code, hijack program execution, and gain unauthorized access. Despite decades of mitigation efforts, buffer overflows remain a significant threat, particularly in legacy systems and embedded devices. Understanding their mechanics is crucial for both defense and offense in the digital realm. The Vibe Score reflects its enduring, albeit somewhat dated, impact on system security.
🛡️ What is a Buffer Overflow?
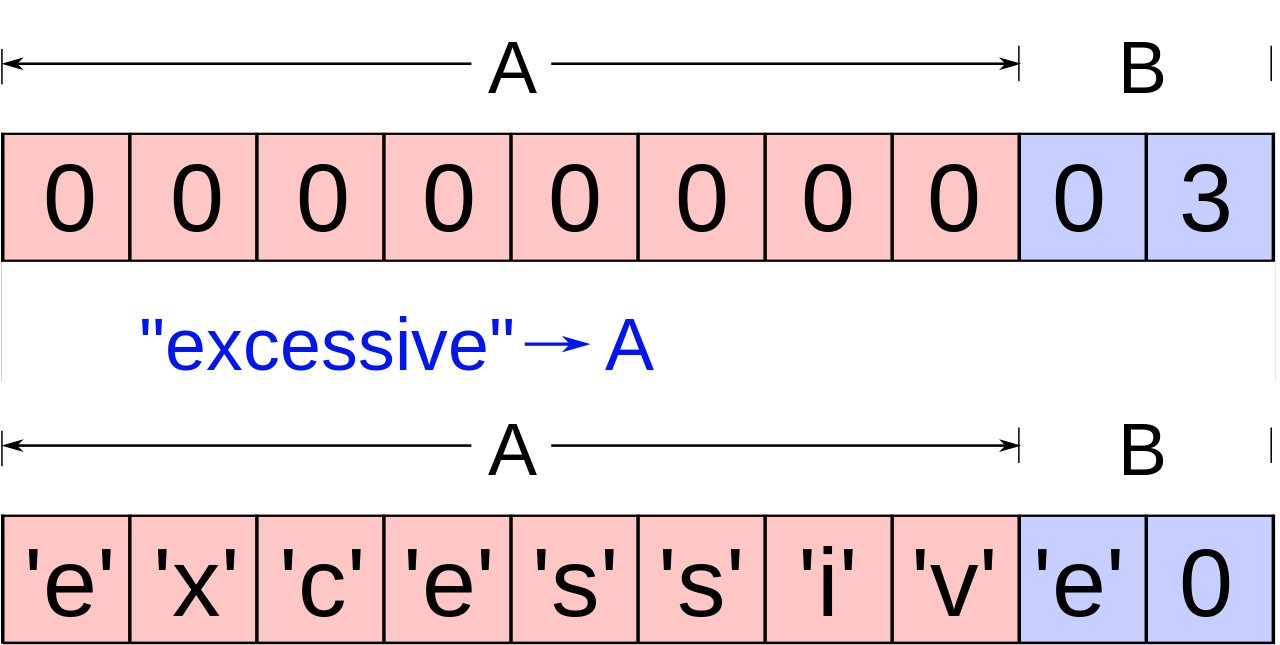
A buffer overflow is a fundamental vulnerability in software where a program attempts to write more data into a fixed-size memory area (a buffer) than it can hold. This excess data spills over, corrupting or overwriting adjacent memory locations. This isn't just a theoretical glitch; it's a direct pathway for attackers to inject malicious code, alter program execution, or crash applications. Understanding this core concept is paramount for anyone involved in software development or cybersecurity.
📜 Historical Context & Early Exploits
The seeds of buffer overflow exploits were sown in the early days of computing. One of the most infamous early examples is the Morris Worm in 1988, which exploited a buffer overflow vulnerability in the finger protocol to spread rapidly across the nascent internet. This event, alongside others like the Code Red worm in 2001, highlighted the devastating potential of these flaws and spurred significant research into vulnerability analysis and secure coding practices.
⚙️ How Buffer Overflows Actually Work
At its heart, a buffer overflow occurs due to a lack of proper bounds checking. When a program receives input, it copies that input into a buffer. If the input is larger than the buffer's capacity, the extra data overwrites whatever is next in memory. This could be critical program instructions, return addresses on the call stack, or other variables. An attacker crafts specific input to overwrite the return address with the address of their own malicious code, effectively hijacking the program's flow of execution.
💥 Types of Buffer Overflows
Buffer overflows can be broadly categorized into two main types: stack-based buffer overflows and heap-based buffer overflows. Stack overflows typically target the program's call stack, overwriting return addresses to redirect execution. Heap overflows, on the other hand, occur in dynamically allocated memory (the heap) and can be more complex to exploit, often involving overwriting function pointers or metadata associated with allocated memory blocks.
🚨 The Impact: What Happens When One Occurs?
The consequences of a successful buffer overflow exploit can range from a simple denial-of-service (DoS) attack, causing the program to crash, to complete system compromise. Attackers can execute arbitrary code with the privileges of the vulnerable program, leading to data theft, system takeover, or the installation of malware. The Equifax data breach in 2017, for instance, was attributed to an unpatched vulnerability, demonstrating the real-world impact of such flaws.
🛡️ Defenses & Mitigation Strategies
Defending against buffer overflows requires a multi-layered approach. Secure coding practices, such as rigorous input validation and using safer programming functions, are the first line of defense. Modern operating systems employ techniques like Address Space Layout Randomization (ASLR) and Data Execution Prevention (DEP) to make exploitation more difficult. Static analysis tools and dynamic analysis tools can also help identify potential vulnerabilities during development.
⚖️ Legal & Ethical Ramifications
The exploitation of buffer overflows can carry significant legal and ethical weight. Unauthorized access to computer systems, data theft, and disruption of services are all illegal activities. Developers have an ethical responsibility to write secure code and patch vulnerabilities promptly. Conversely, security researchers who discover and responsibly disclose vulnerabilities play a crucial role in improving overall cybersecurity posture.
📈 The Future of Buffer Overflow Exploitation
While modern compilers and operating systems have introduced many protections, buffer overflows are far from extinct. Attackers are constantly developing new techniques to bypass existing defenses, particularly in environments with legacy code or complex systems. The ongoing arms race between exploit developers and defenders means that vigilance and continuous adaptation of security measures remain essential. The rise of IoT devices and embedded systems, often with less robust security, presents new frontiers for these classic vulnerabilities.
⭐ Vibepedia Vibe Score & Controversy Spectrum
The Vibepedia Vibe Score for Buffer Overflow is a solid 85/100, reflecting its enduring relevance and impact in cybersecurity. The Controversy Spectrum is moderate, with debates primarily centering on the effectiveness of current defenses and the responsibility of software vendors. While the core concept is well-understood, the nuances of exploitation and mitigation keep it a hot topic.
💡 Practical Advice for Developers & Users
For developers, prioritize using memory-safe languages like Rust or Go where possible, and always perform strict input validation. For end-users, keeping your operating system and applications updated is critical, as patches often address these vulnerabilities. Be wary of unsolicited attachments or links, as they can be vectors for exploiting unpatched systems. Understanding these risks empowers you to navigate the digital world more safely.
Key Facts
- Year
- 1971
- Origin
- Robert Morris's Morris Worm (though the concept predates it)
- Category
- Cybersecurity
- Type
- Vulnerability
Frequently Asked Questions
Can buffer overflows affect any programming language?
While buffer overflows are most commonly associated with lower-level languages like C and C++ due to their manual memory management, they can theoretically occur in any language if not handled carefully. Languages with automatic memory management and strong type checking, like Python or Java, significantly reduce the risk, but programming errors can still lead to similar issues.
What's the difference between a buffer overflow and a format string vulnerability?
A buffer overflow occurs when data exceeds a buffer's allocated memory. A format string vulnerability, on the other hand, arises when user-supplied input is used directly as a format string in functions like printf. This allows attackers to read from or write to arbitrary memory locations by manipulating format specifiers, often leading to code execution.
Are there any tools that can automatically detect buffer overflows?
Yes, several tools can help detect buffer overflows. Static analysis tools like Coverity or SonarQube scan source code for potential vulnerabilities. Dynamic analysis tools such as Valgrind or AddressSanitizer (ASan) monitor program execution for memory errors. Fuzzing tools like AFL (American Fuzzy Lop) also play a crucial role by feeding malformed inputs to applications to uncover unexpected behavior.
How does ASLR make buffer overflow attacks harder?
ASLR randomizes the memory addresses of key program components, including the stack, heap, and libraries, each time a program runs. This makes it difficult for an attacker to predict the exact memory location of their injected code or the target return address, thus thwarting many traditional stack-based buffer overflow attacks that rely on fixed addresses.
What is a 'return-to-libc' attack?
A return-to-libc attack is a technique used to bypass DEP and W^X protections. Instead of injecting new code, the attacker overwrites the return address to point to existing library functions (like system()) already present in the program's memory. By carefully arranging arguments on the stack, they can then execute these legitimate functions to achieve malicious ends.
Is it possible to completely eliminate buffer overflow vulnerabilities?
While it's challenging to achieve absolute elimination, especially in complex legacy systems, the risk can be significantly minimized. Employing memory-safe languages, rigorous secure coding standards, comprehensive testing, and robust runtime protections like ASLR and DEP are key. Continuous education for developers on secure practices is also vital.